What continuous cloud compliance tools can I use? Part 2
Individual cloud environments offer a set of tools with which you can largely cover the area of continuous cloud compliance. Unlike ready-made solutions, you may have to connect the individual tools to each other yourself, integrate them into your existing SIEM tool, or similar. But in the context of the cost of ready-made solutions, these will be marginal amounts.
On the other hand, you need to have some know-how and an idea of what you want to achieve. Let's look at the tools you can immediately deploy and use in each cloud environment. The following list certainly does not have the ambition to cover all the tools offered, but to present those that I personally consider to be the most important.

Amazon Web Services & Continuous Cloud Compliance
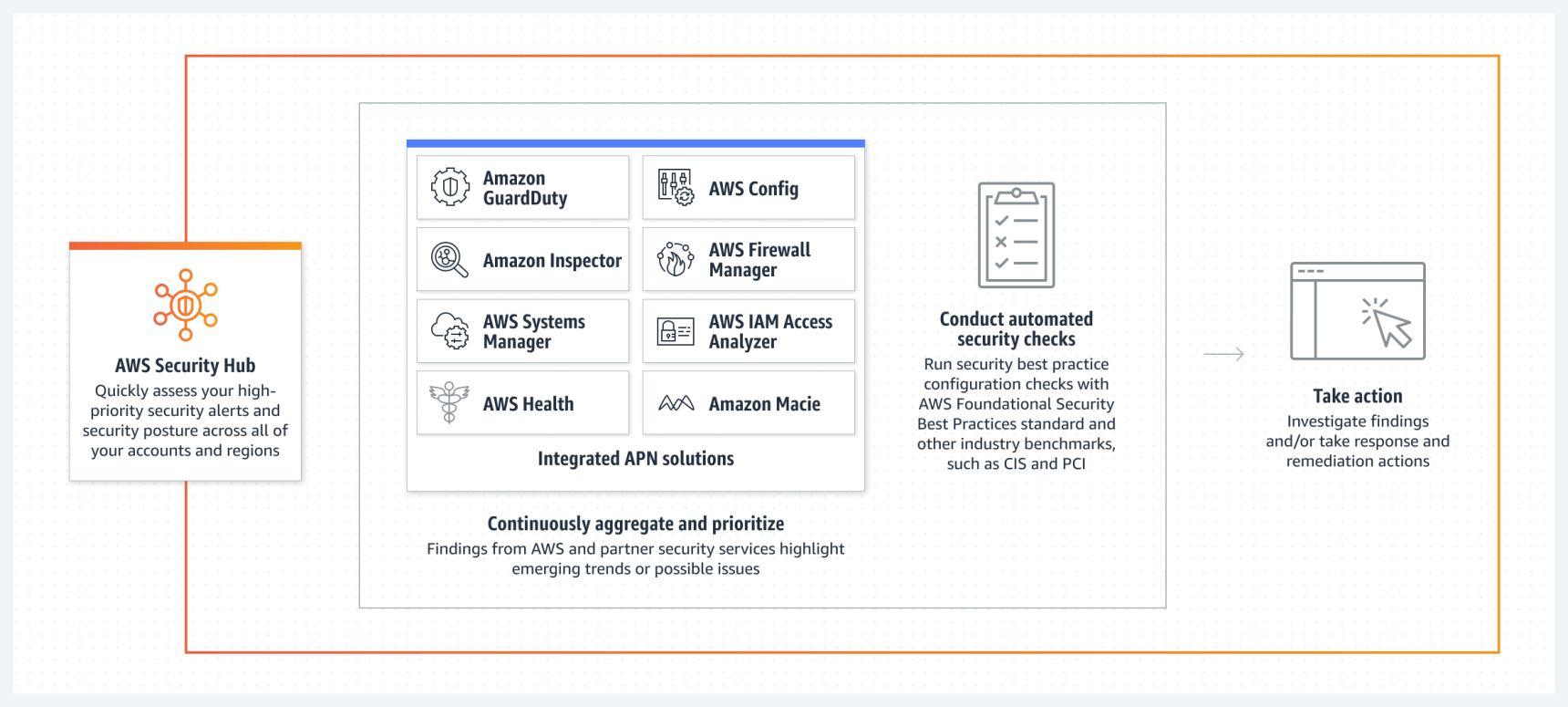
AWS Security Hub provides a central view of all security-related areas in AWS and brings together other tools (e.g. the results of automated infrastructure scans with Amazon Inspector or sensitive data identified by Amazon Macie).
Source: Amazon Web Services
AWS Config
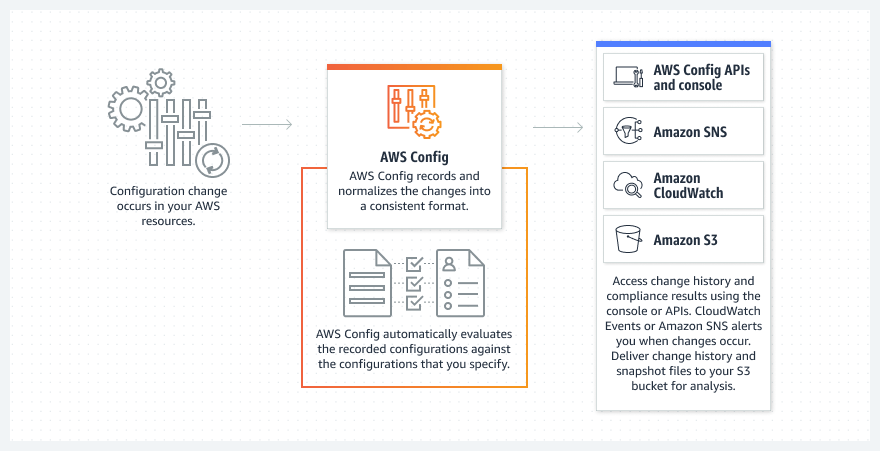
AWS Config is an asset management service. It makes it possible to evaluate the status of individual sources against defined security policies.
Source: Amazon Web Services
AWS Inspector
AWS Inspector allows you to perform automated scanning of various operating components (virtual servers, containers, container images) against known vulnerabilities (CVEs).
Source: Amazon Web Services

Amazon GuardDuty
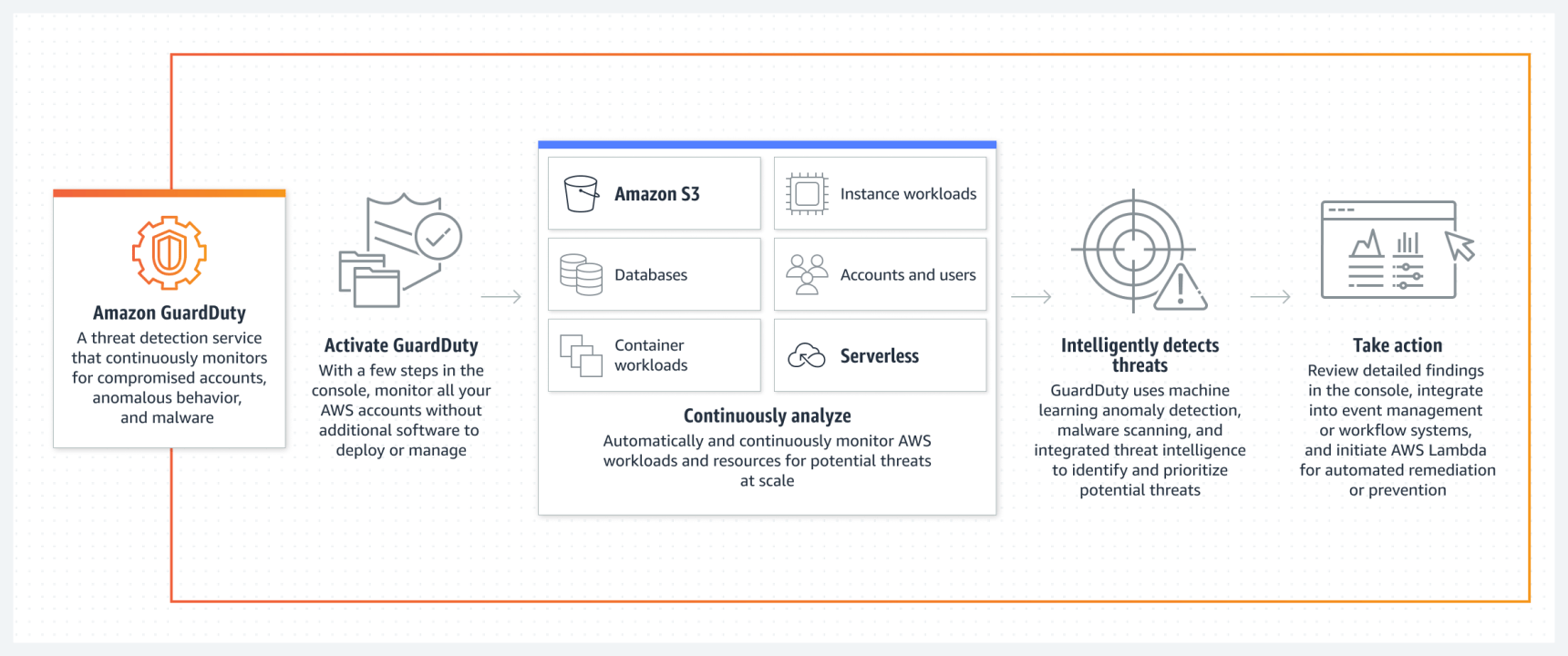
Amazon GuardDuty allows you to automatically analyze individual logs or audit trails. Based on anomaly detection and machine learning, it alerts you to potential security incidents.
Source: Amazon Web Services
Microsoft Azure & Continuous cloud compliance
Azure Policy allows you to define (and possibly enforce) individual security policies over operated components.
Microsoft Defender for Cloud
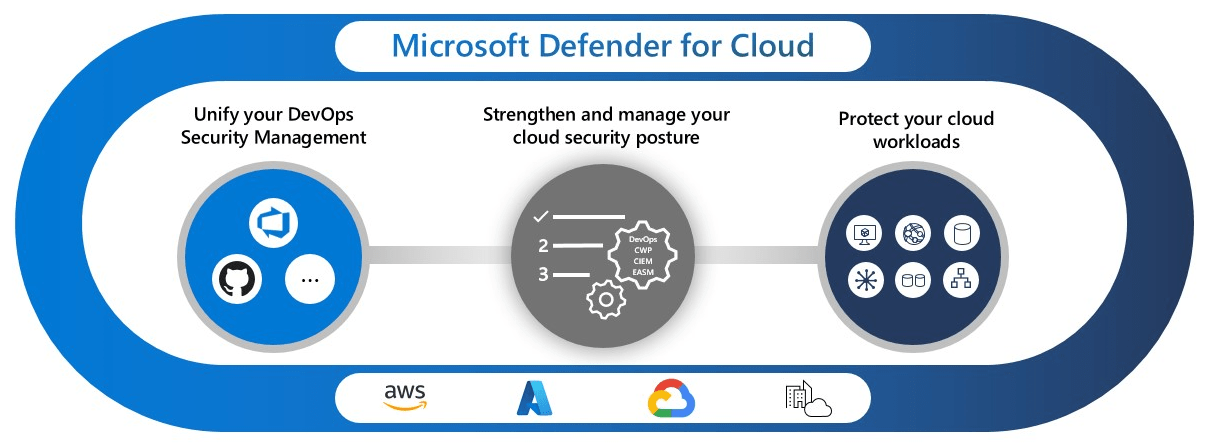
Microsoft Defender for Cloud is a de facto comprehensive cloud security posture management tool (similar to third-party products) covering various areas of continuous cloud compliance.
Defender for Cloud (Source: Microsoft)
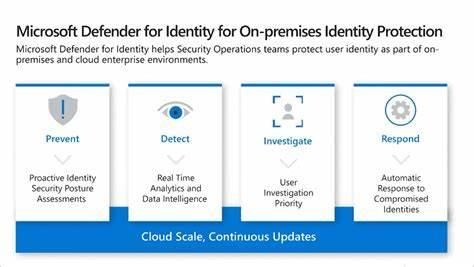
Microsoft Defender for Identity
Microsoft Defender for Identity provides a wide range of identity protection services. For example, it can reveal compromised identities (e.g. a misused serviceaccount, etc.).
Defender for Identity (Source: Microsoft)
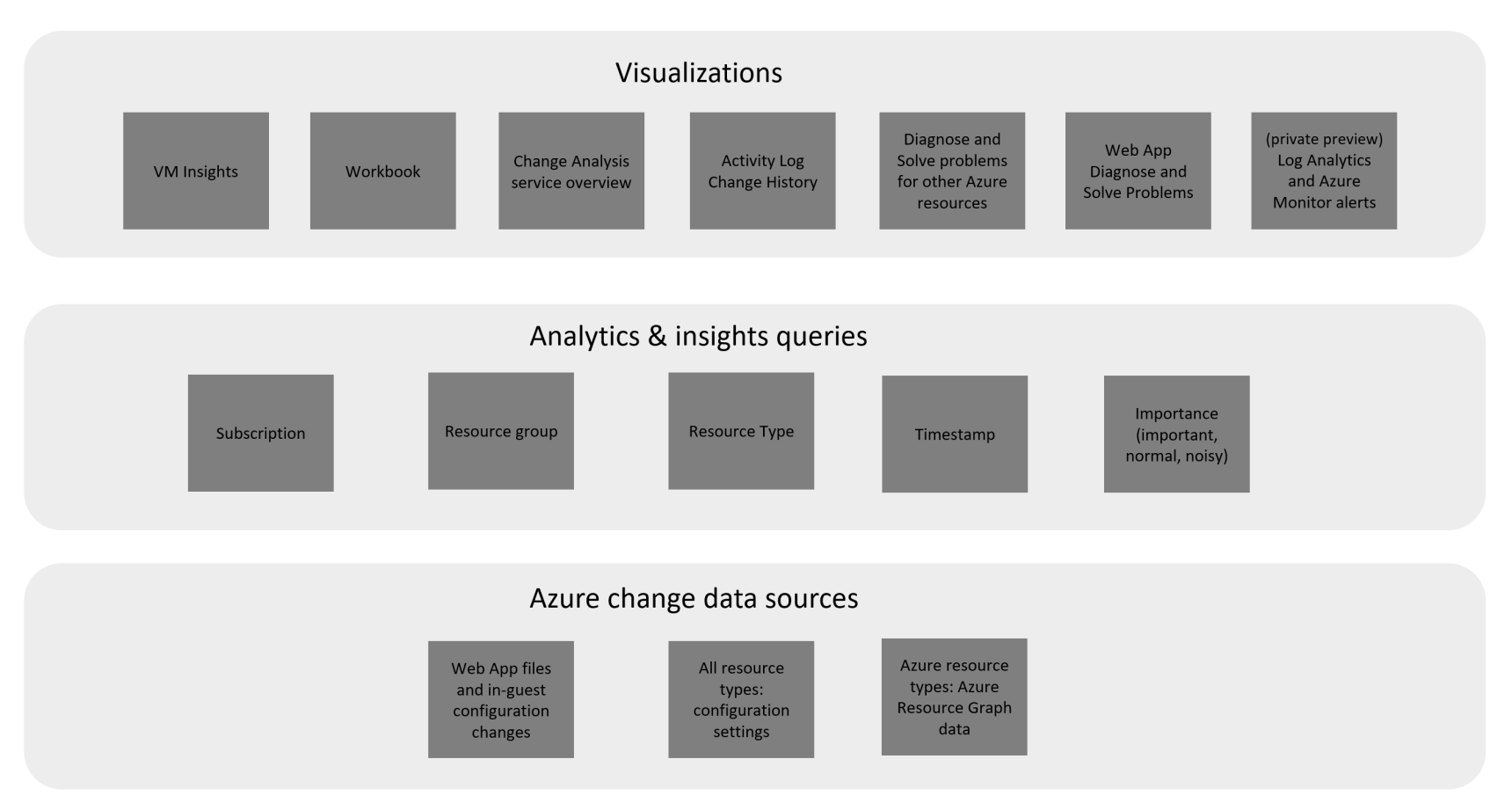
Application Change Analysis
Application Change Analysis allows you to inventory all operating resources and track any configuration changes made.
Application Change Analysis (Source: Microsoft)
Third party products
Personally, I prefer to use the tools provided by the cloud providers themselves, which I can tailor exactly to my needs. But it takes some effort and, as we know, time is money. Therefore, in some cases, it is preferable if you reach for ready-made third-party solutions.
In the case of ready-made solutions, I see a certain discrepancy between the required and provided functionality and several other pros and cons.
Benefits of ready-made solutions:
- They are usually provided as SaaS without the need to "worry" about the tool as such
- Seamless integration of different cloud providers, at least for AWS and Azure
- Simple and fast deployment; Basic onboarding environment is a matter of minutes
- A unified view of different cloud environments
- Extensive functionality provided
Disadvantages of ready-made solutions:
- They provide as-is functionality. If something doesn't suit you, it's difficult or impossible to change it.
- In some cases, the pricing model is complicated (payment for various modules, functional units, etc.).
- The price is usually based on the number of "managed" resources.
If, after this quick evaluation, you are more inclined to use third-party tools, I would recommend taking a look at least at the following products:
- Check Point CloudGuard
- Wiz.io
- Datadog
- Orca Security
I don't want to go into complex evaluations of individual products, because only your requirements may differ significantly from the expectations I have from similar products. On a general level, I personally gravitate primarily towards CloudGuard, which I know from the times when it was not a Check Point product, but a Dome9 product or Wiz.io that has recently seen a lot of explosive growth.
Closing thoughts on continuous cloud compliance
What should you take away from this article?
First and foremost, security in the cloud is entirely your responsibility. As a result, you should always be aware of the condition of the individual components in operation and be able to define your individual safety policies and requirements.
From my point of view, it doesn't matter which continuous cloud compliance tools you use. But if you're migrating production applications to the cloud, you should be able to cover this area.
If you are considering deploying continuous cloud compliance and would like to discuss the topic in greater detail (technical capabilities of individual products, necessary process changes that will certainly have to occur, etc.), feel free to contact us and we will try to come up with the best solution for your individual needs.
Need assistance? We're here for you!